Use Case
Remote Access
Reach internal systems from anywhere with identity-based access — without exposing private infrastructure or granting broad network access.

Internal systems become part of the attack surface when exposed to the public internet
What starts as a practical need, reaching internal systems from outside the corporate network, often turns into broader exposure than necessary. Admin interfaces, VPN gateways, remote desktops, internal applications, dashboards, and critical services become reachable by more users, networks, or the public internet than the task actually requires. That exposure matters because vulnerabilities in internet-facing software, edge devices, and remote-access systems are increasingly exploited before traditional patching processes can catch up.
average time from vulnerability disclosure to confirmed exploitation, down from 56 days in 2024.
of vulnerability-exploitation targets in breach data were edge devices and VPNs, up from 3% one year earlier.
rank lateral movement as a top concern with VPN-based access models.
publicly exposed VNC servers had authentication disabled.
The Zero Day Clock tracks annual Time-to-Exploit trends, estimating the gap between public CVE disclosure and observed exploitation using datasets such as CISA KEV, VulnCheck KEV, and XDB. Its annual estimate uses a 10% trimmed mean.
Verizon's 2025 Data Breach Investigations Report analyzed 22,052 security incidents and 12,195 confirmed data breaches. It found that exploitation of vulnerabilities reached 20% of known initial access vectors in breaches, a 34% increase from the prior report. Verizon states that this growth was supported in part by zero-day exploits targeting edge devices and VPNs. Edge devices and VPNs accounted for 22% of vulnerability-exploitation targets, up from 3% in the prior report; only about 54% of those vulnerabilities were fully remediated during the year, with a median remediation time of 32 days.
The ThreatLabz 2025 VPN Risk Report is based on a global survey of 632 IT and cybersecurity professionals. Zscaler reports that 89% of respondents are concerned about attackers moving laterally across the network and that 71% rank lateral movement as a top concern. The report links this concern to VPNs' implicit-trust model, where one compromised user can gain broad network reachability rather than narrowly scoped application or service access.
Forescout Research - Vedere Labs used Shodan to analyze publicly exposed RDP and VNC remote-access services. It found more than 1.8 million exposed RDP servers and more than 1.6 million exposed VNC servers globally. More specifically, it found almost 60,000 exposed VNC servers with authentication disabled, including more than 670 that provided direct access to OT/ICS control panels. Forescout states that disabled authentication allows anyone to interact with the applications presented by the device, making this a strong example of remote access exposure that is broader than intended or safe.
Access should depend on identity and policy, not network location
Grant access based on identity, device posture, and explicit policy, so employees, admins, contractors, and service accounts can reach only the systems they are allowed to use without making private infrastructure publicly reachable.
Control access through users, groups, and roles
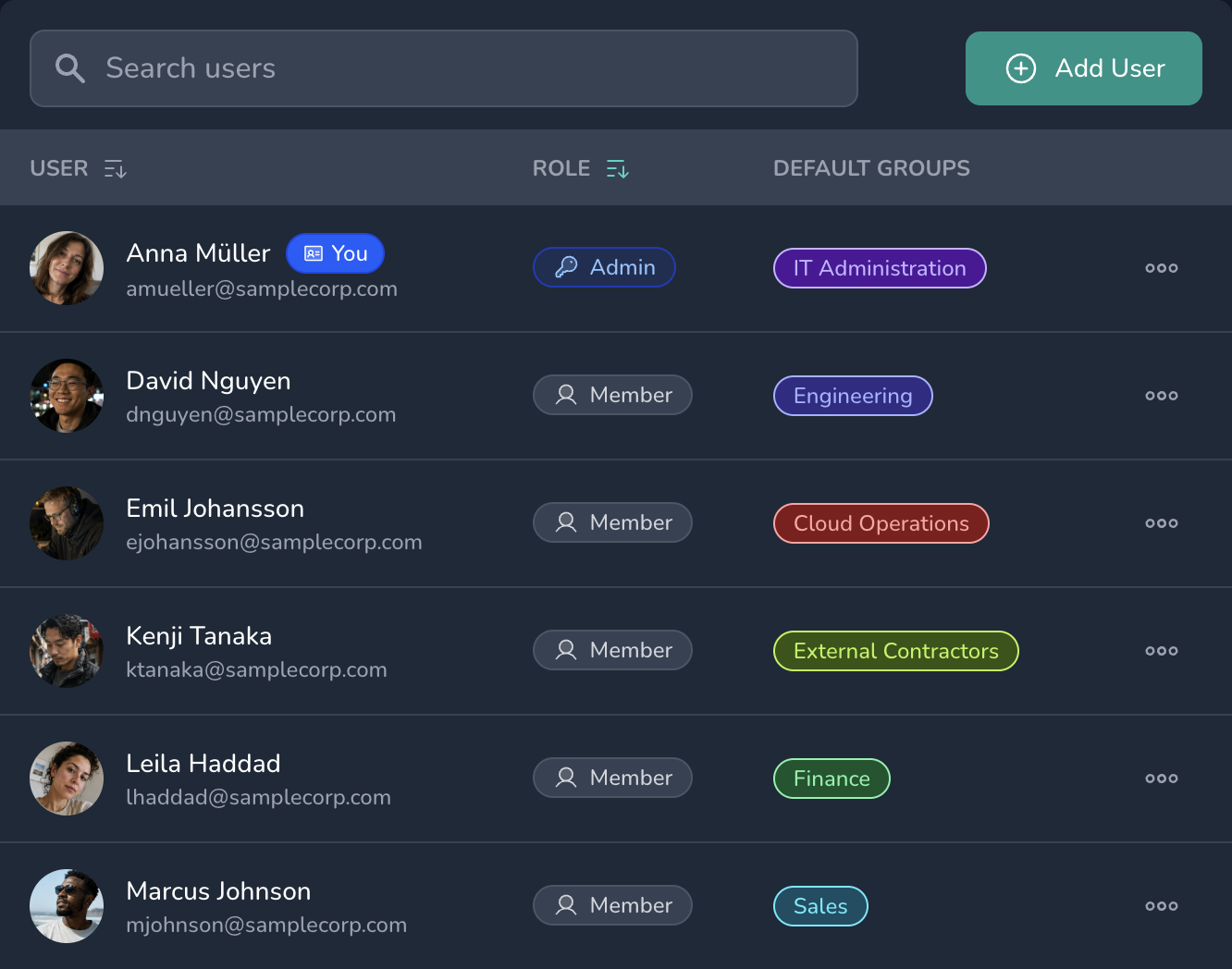
Remote access becomes identity-based. Permissions follow users, groups, and roles instead of static VPN profiles, shared network access, or low-level IP rules.
- User-based access Grant access based on who someone is and which role or group they belong to.
- IdM integration Keep permissions aligned with your organization’s identity management system.
- Single source of truth Review users, groups, and access policies from one central controller.
Replace low-level rules with readable access policies
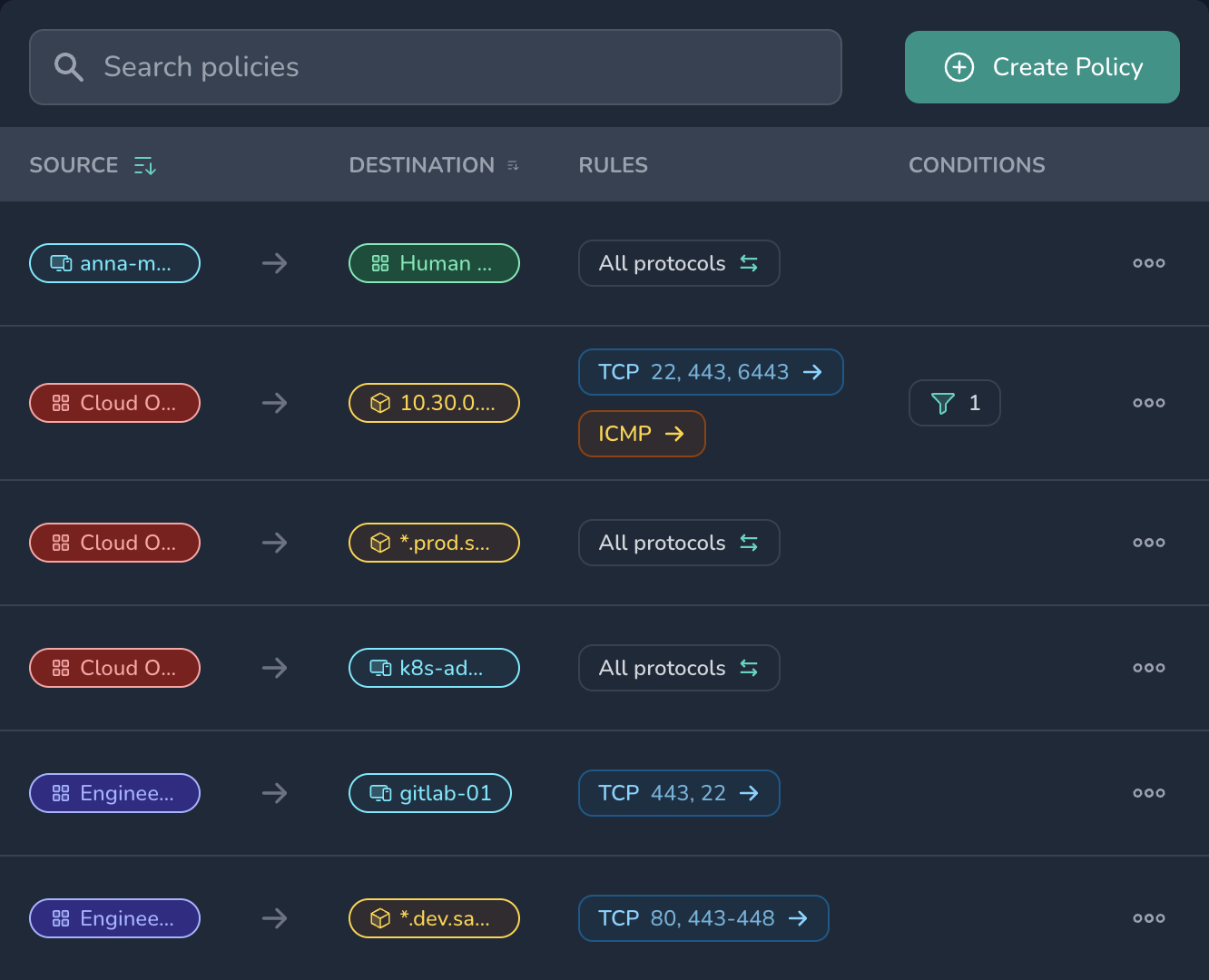
Define access as organizational intent: who should reach which resource. Policies stay readable in the controller instead of being scattered across IP rules, firewall exceptions, and VPN configuration.
- Intent-based policies Describe who should reach which resource without translating every decision into low-level network rules.
- Web-based control Manage access policies centrally instead of spreading decisions across firewalls, VPN profiles, and local configuration.
- Explainable access Preview who can reach which resource and which policy grants that access.
Bring Zero Trust Network Access to your organization
Netsody helps organizations keep internal systems private while granting access by identity, device, and policy. Manage users, devices, groups, routes, and revocation from one controller instead of spreading access decisions across VPN profiles, firewall rules, and local accounts.
- Private systems stay private Avoid public entry points for internal applications, admin consoles, dashboards, and remote desktops.
- Access follows identity Grant access based on users, devices, groups, roles, and explicit policies.
- Least privilege by default Give users access to the resources they need, not broad reachability across the network.
- Control stays central Review, change, and revoke access from one web-based controller.
