Use Case
Business VPN
Give employees, sites, cloud workloads, and internal services one centrally governed private network.
- Secure remote access to internal tools and private services.
- Connect sites, cloud workloads, and routed resources in one model.
- Manage users, devices, and policies from one controller.

The Enterprise Access Problem
The real problem is not the VPN. It is the access sprawl around it
Modern enterprise access rarely fails because of one missing tunnel. It becomes hard to control because every new employee group, branch, cloud workload, contractor, and private service adds another way into the environment.
VPN gateways, IPsec tunnels, firewall ACLs, admin gateways, split DNS, SSO groups, MDM checks, and ticket workflows each carry a piece of the answer. The result is more admin work, more cost, and no single place that can reliably answer who can reach what right now.
of organizations have experienced a VPN-related cyberattack.
report user dissatisfaction with VPNs due to slow connections, cumbersome authentication, or frequent disconnections.
median time to fully remediate edge-device vulnerabilities.
plan to replace VPN services with Zero Trust access models within one year.
The 2025 VPN Exposure Report is based on a survey of 648 IT, network, and cybersecurity professionals. It found that 48% of organizations have experienced a VPN-related cyberattack, with attackers exploiting stolen credentials, zero-day vulnerabilities, and VPN misconfigurations.
The 2025 VPN Exposure Report is based on a survey of 648 IT, network, and cybersecurity professionals. It found that 83% report user dissatisfaction with VPNs due to slow connections, cumbersome authentication, and frequent disconnections. The report frames these issues as productivity problems that can push users toward insecure workarounds.
Verizon's 2025 Data Breach Investigations Report found that edge devices and VPNs accounted for 22% of vulnerability-exploitation targets, up from 3% in the prior report. Only about 54% of these vulnerabilities were fully remediated during the year, with a median remediation time of 32 days.
The ThreatLabz 2025 VPN Risk Report with Cybersecurity Insiders draws on insights from more than 600 IT and security professionals. Zscaler reports that 65% of organizations plan to replace VPN services within the year, reflecting a broader shift toward Zero Trust access models.
Manage access by user and group, not by subnet
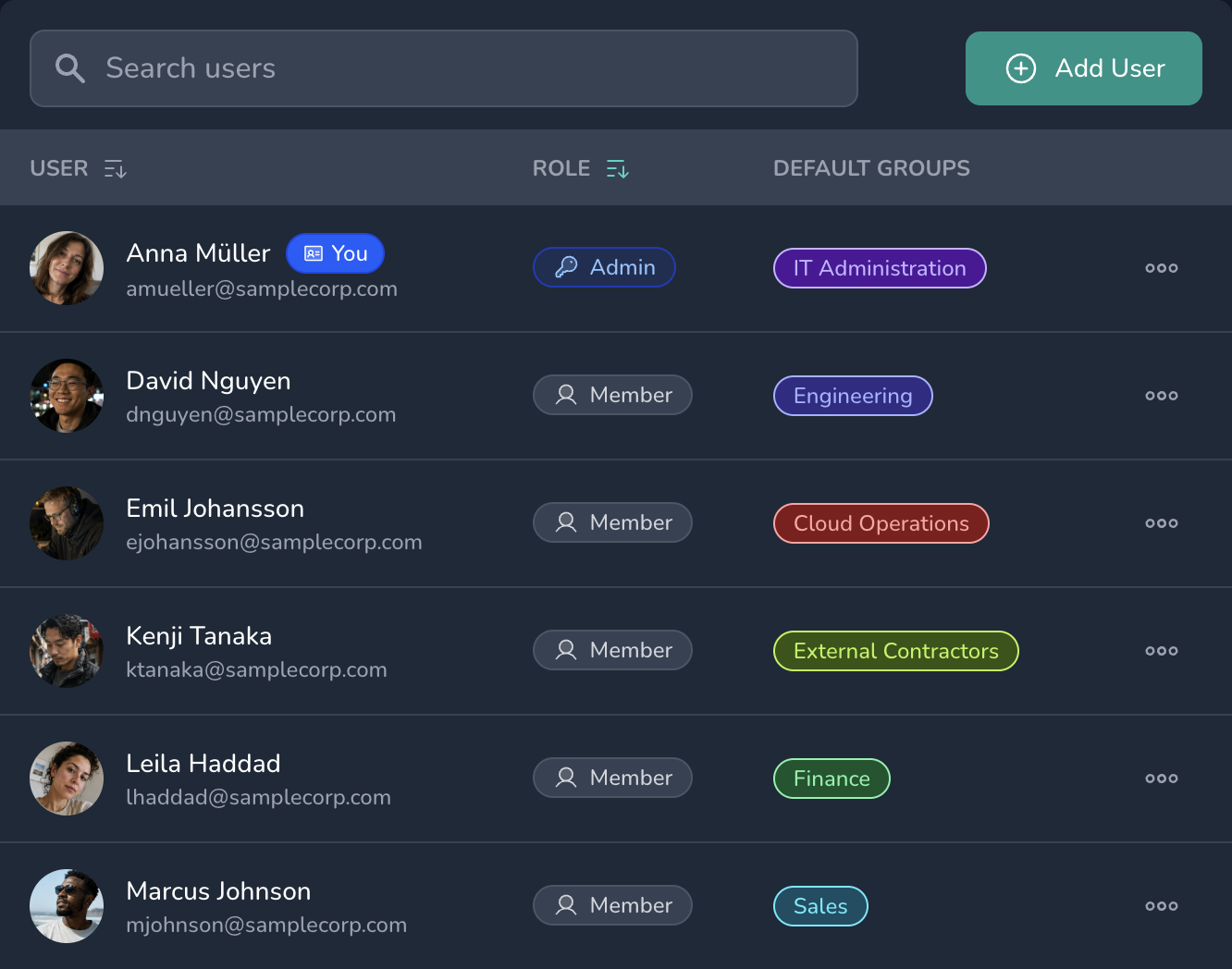
Keep permissions explicit as the network grows
From VPN patchwork to governed private access
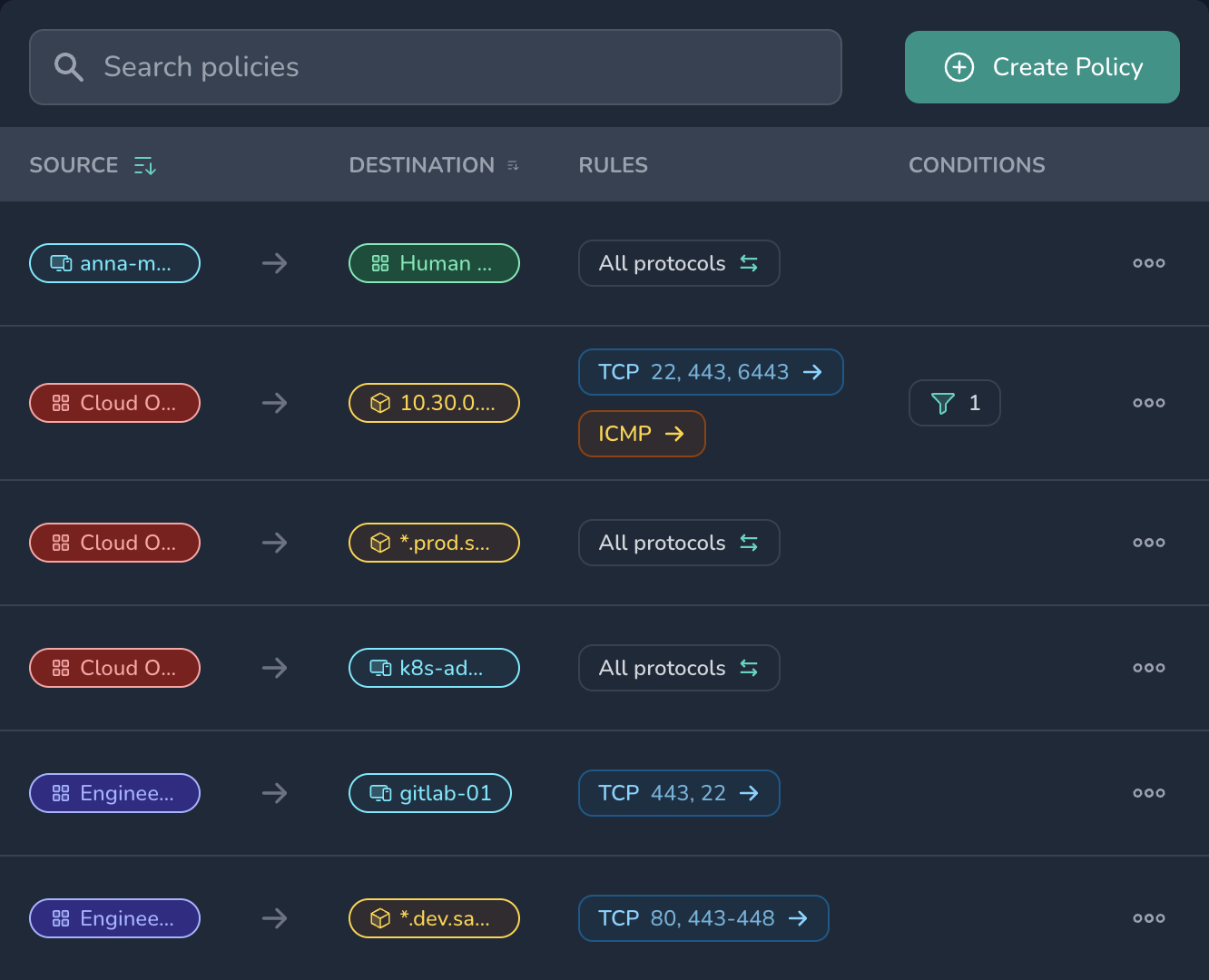
Netsody replaces the usual patchwork of VPN gateways, firewall exceptions, site tunnels, admin gateways, and one-off access tools with one governed Zero Trust network. Teams manage employees, devices, sites, cloud workloads, and private services in one place instead of spreading critical access decisions across separate consoles.
That matters because access sprawl is not only inconvenient. It creates stale exceptions, broad network paths, unclear ownership, and expensive manual work every time a team, vendor, service, route, or office changes.
Business VPNs become difficult when access logic spreads
- Remote access, site connectivity, cloud access, and contractor access often end up in separate systems with different owners.
- Access becomes broader than it should be once someone is connected, because network reachability is easier to grant than precise service access.
- Firewall rules, VPN profiles, DNS entries, group memberships, and jump-host permissions drift apart over time.
- Every change in teams or infrastructure creates extra admin work, more tickets, and another chance to leave access open.
Access needs to stay visible and controllable
- Central management: Keep users, devices, groups, routes, resources, and policies in one controller.
- Zero Trust access: Decide who may reach which private service before the network path opens, with support for user management and MFA.
- Direct private paths: Use encrypted, direct paths that avoid central VPN bottlenecks and stay usable where legacy VPN protocols are blocked.
- Straightforward rollout: Add users and devices incrementally across Windows, macOS, Linux, iOS, Android, and Docker-based environments.
One platform for common business access needs
- Remote employees reaching internal tools.
- Connecting offices, smaller sites, and cloud resources.
- Limited access for contractors or external admins.
Ready to secure your network with Netsody?
Tell us about your environment and what you want to connect. We’ll help you take the first step toward Zero Trust Network Access.
